Beta This feature is in beta and might change in the future.
We're very much looking for input and feedback on this feature. You can either contact us directly, file an issue, or tweet at us.
Executors are Sourcegraph's solution for running untrusted code in a secure and controllable way.
To deploy executors to target your Sourcegraph instance, follow our deployment guide.
There are two supported installation paths (in Beta):
- Beta Deploy with Terraform on AWS or GCP. Sourcegraph provides Terraform modules and AMIs for supported regions.
- Beta Deploy binaries.
There are two supported installation methods (Experimental):
- Experimental Deploy on Kubernetes via Helm or manifests.
- Experimental Deploy via Docker-Compose.
NOTE: Note to all Technical Success team members: please reach out to the product and engineering teams in #wg-shipping-executors for any discussion about deployment modes other than the two documented paths above. We expect large customers (Large Enterprise and Strategic) to have complex and heterogenous requirements not addressed by the deployment models currently in Beta out of the box. Reach out in #wg-shipping-executors early in the process to collect requirements and discuss present and future implementation options.
Running untrusted code is a core requirement of features such as precise code navigation auto-indexing, and running batch changes server-side.
Auto-indexing jobs, in particular, require the invocation of arbitrary and untrusted code to support the resolution of project dependencies. Invocation of post-install hooks, use of insecure package management tools, and package manager proxy attacks can create opportunities in which an adversary can gain unlimited use of compute or exfiltrate data. The latter outcome is particularly dangerous for on-premise installations of Sourcegraph, which is the chosen option for companies wanting to maintain strict privacy of their code property.
Instead of performing this work within the Sourcegraph instance, where code is available on disk and unprotected internal services are available over the local network, we move untrusted compute into a sandboxed environment, the executor, that has access only to the clone of a single repository on disk (its workspace) and to the public internet.
Executor instances are capable of being deployed in a variety of ways. Each runtime vary in how jobs are executed.

- User run the
src(e.g.src batch) command from the command line. srccalls the Sourcegraph API to clone a repository.- The repositories are written to a directory.
- A Docker Container is created for each "step."
- The directory containing the repository is mounted to the container.
- "Steps" are ran in sequential order.
- The container run a defined command against the repository.
- Logs from the container are sent back to
src. - At the end of processing all repositories, the result is sent to a Sourcegraph API.
- e.g. Batch Changes sends a
git diffto a Sourcegraph API (and invokes other APIs).
- e.g. Batch Changes sends a
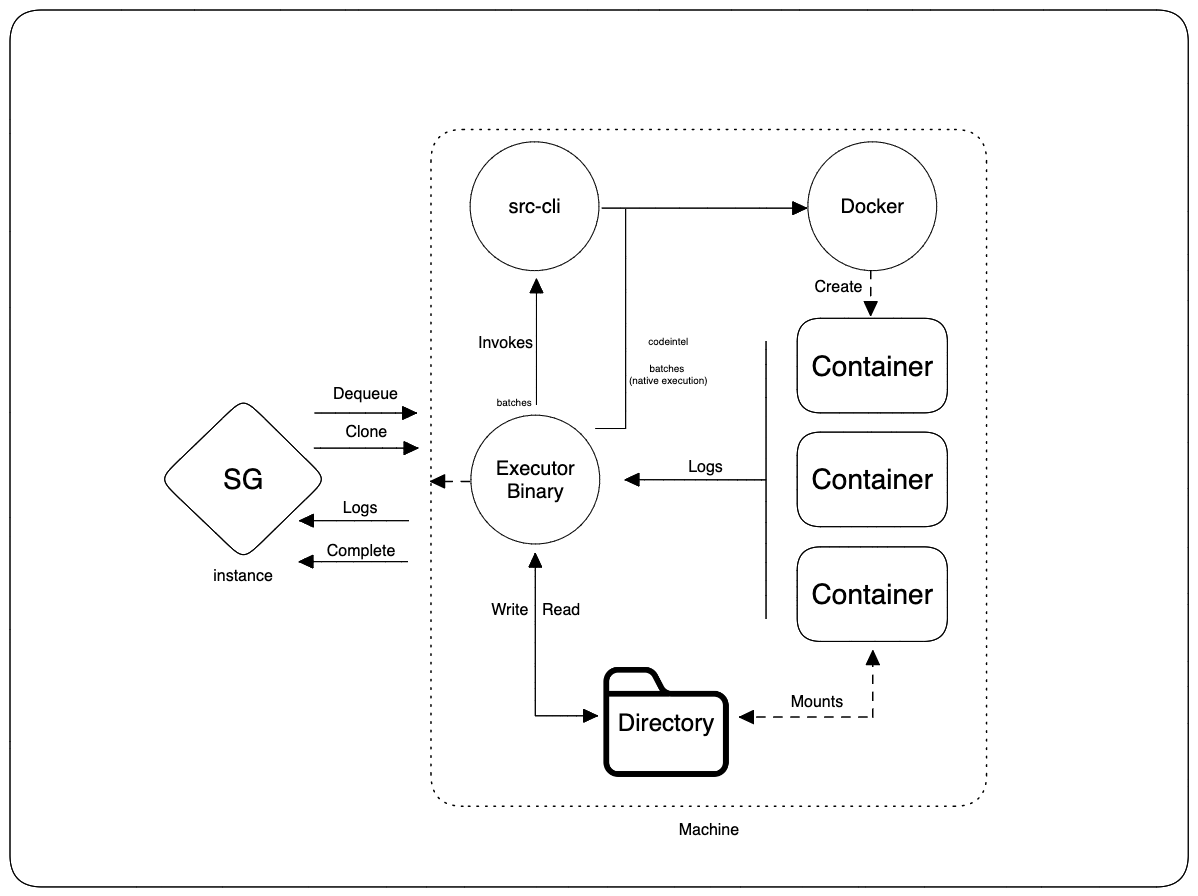
- The executor binary is installed to a machine.
- Additional executables (e.g. Docker,
src) are installed as well
- Additional executables (e.g. Docker,
- The executor instances pulls for available Jobs from a Sourcegraph API
- A user initiates a process that creates executor Jobs.
- The executor instance "dequeues" a Job.
- Executor calls the Sourcegraph API to clone a repository.
- The repositories are written to a directory.
- A Docker Container is created for each "step."
- If the Job is
batches(non-native execution),srcis invoked - Docker is invoked directly for other Jobs (
codeinteland native executionbatches) - The directory containing the repository is mounted to the container.
- "Steps" are ran in sequential order.
- If the Job is
- The container run a defined command against the repository.
- Logs from the container are sent back to the executor.
- Logs are streamed from the executor to a Sourcegraph API
- The executor calls a Sourcegraph API to that "complete" the Job.
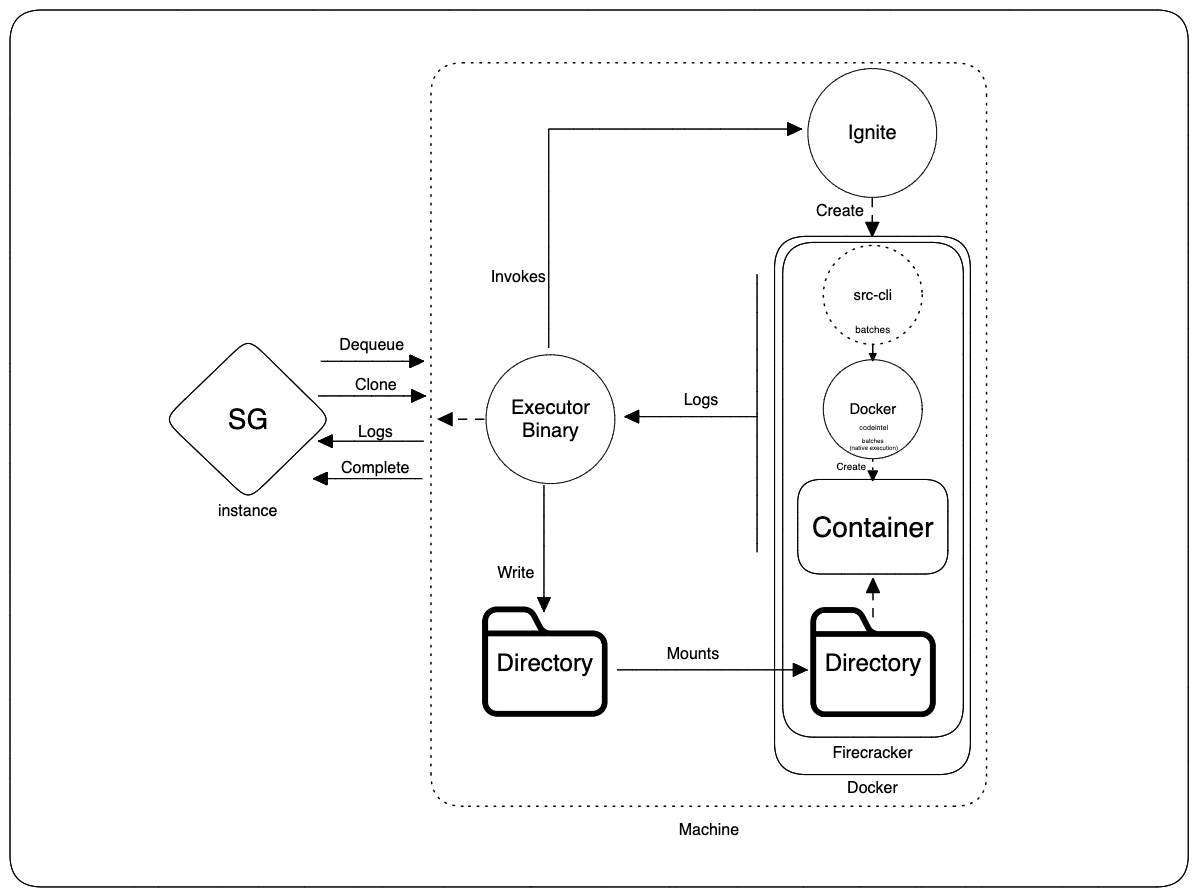
- The executor binary is installed to a machine.
- Additional executables (e.g. Docker,
src) are installed as well
- Additional executables (e.g. Docker,
- The executor instances pulls for available Jobs from a Sourcegraph API
- A user initiates a process that creates executor Jobs.
- The executor instance "dequeues" a Job.
- Executor calls the Sourcegraph API to clone a repository.
- The repositories are written to a directory.
ignitestarts up a Docker container that spawns a single Firecracker VM within the Docker container.- The directory containing the repository is mounted to the VM.
- Docker Container is created in the Firecracker VM for each "step."
- If the Job is
batches(non-native execution),srcis invoked - Docker is invoked directly for other Jobs (
codeinteland native executionbatches) - "Steps" are ran in sequential order.
- If the Job is
- Within each Firecracker VM a single Docker container is created
- The container run a defined command against the repository.
- Logs from the container are sent back to the executor.
- Logs are streamed from the executor to a Sourcegraph API
- The executor calls a Sourcegraph API to that "complete" the Job.
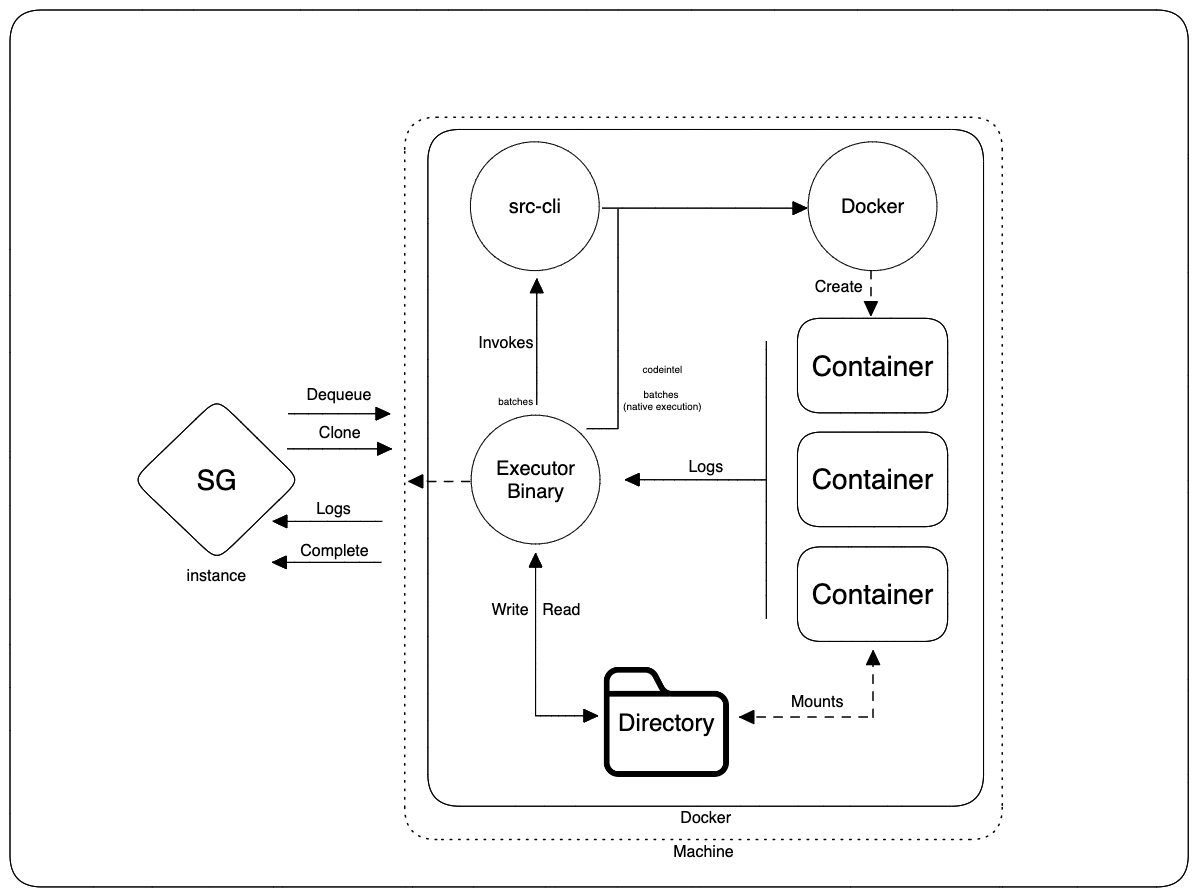
- The executor image is started as a Docker container on a machine
- The executor pulls for available Jobs from a Sourcegraph API
- A user initiates a process that creates executor Jobs.
- The executor instance "dequeues" a Job.
- Executor calls the Sourcegraph API to clone a repository.
- The repositories are written to a directory.
- A Docker Container is created for each "step."
- If the Job is
batches(non-native execution),srcis invoked - Docker is invoked directly for other Jobs (
codeinteland native executionbatches) - The directory containing the repository is mounted to the container.
- "Steps" are ran in sequential order.
- If the Job is
- The container run a defined command against the repository.
- Logs from the container are sent back to the executor.
- Logs are streamed from the executor to a Sourcegraph API
- The executor calls a Sourcegraph API to that "complete" the Job.
Experimental
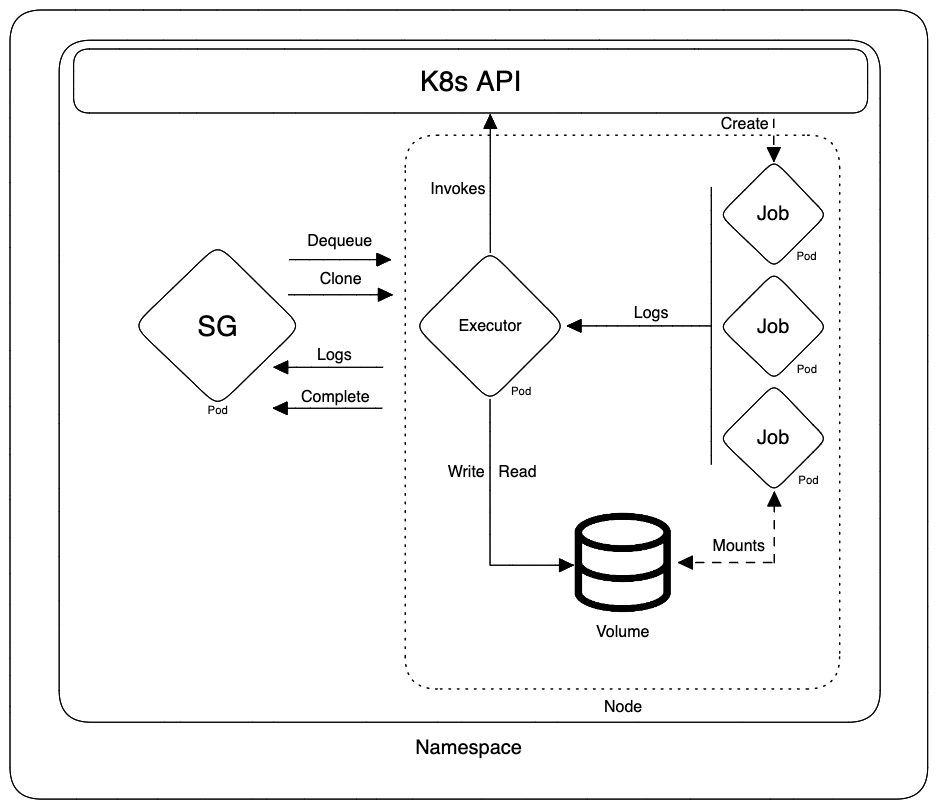
- The executor image is started as a pod in a Kubernetes node
- The executor pulls for available Jobs from a Sourcegraph API
- A user initiates a process that creates executor Jobs.
- The executor instance "dequeues" a Job.
- Executor calls the Sourcegraph API to clone a repository.
- The repositories are written to a directory.
- A Kubernetes Job is created for each "step."
- The directory containing the repository is mounted to the container.
- "Steps" are ran in sequential order.
- The container run a defined command against the repository.
- Logs from the container are sent back to the executor.
- Logs are streamed from the executor to a Sourcegraph API
- The executor calls a Sourcegraph API to that "complete" the Job.
Experimental
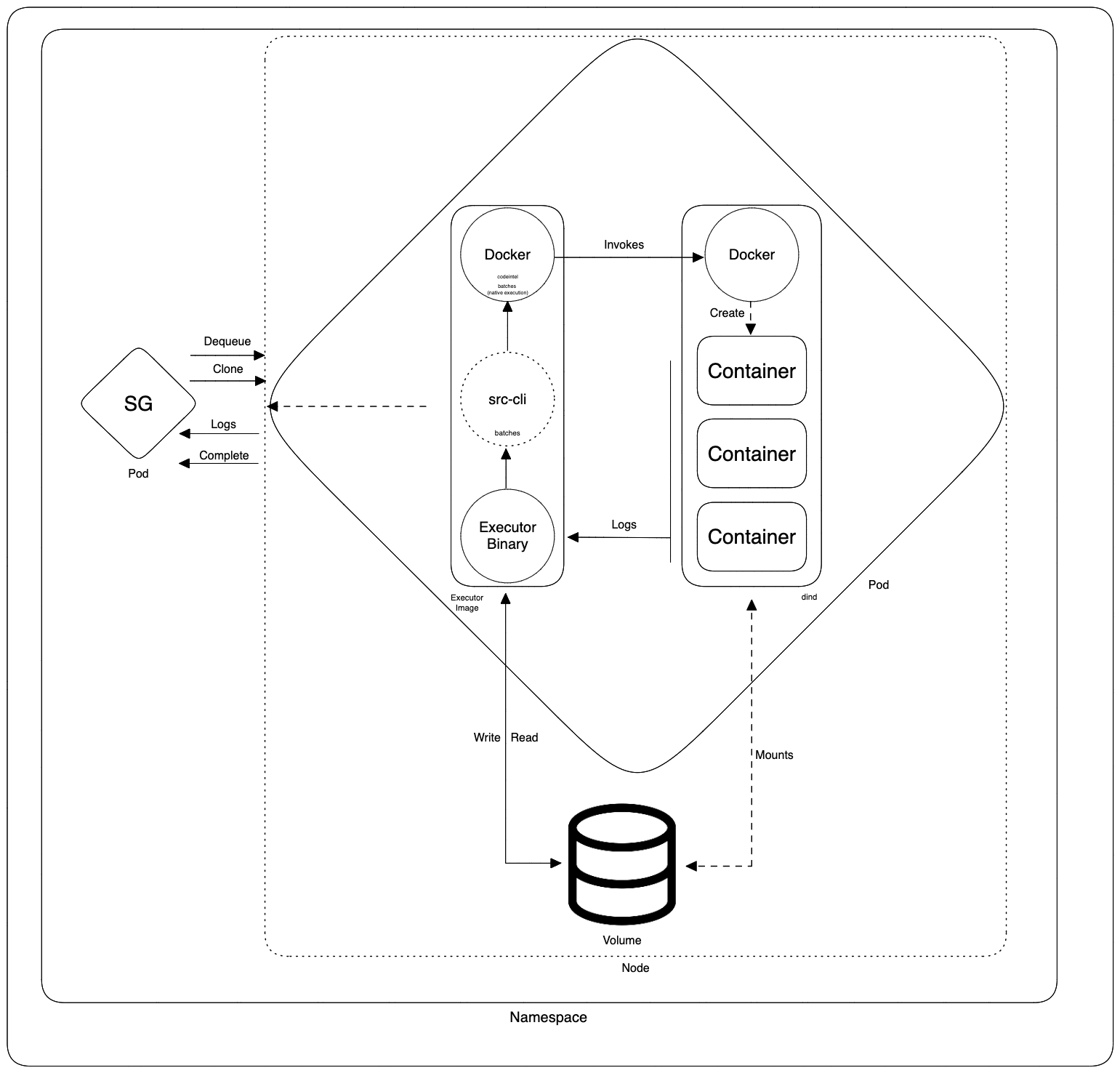
- The executor image is started as a container in Kubernetes Pod
- The dind image is started as a sidecar container in the same Kubernetes Pod
- The executor pulls for available Jobs from a Sourcegraph API
- A user initiates a process that creates executor Jobs.
- The executor instance "dequeues" a Job.
- Executor calls the Sourcegraph API to clone a repository.
- The repositories are written to a directory.
- A Docker Container is created for each "step."
- If the Job is
batches(non-native execution),srcis invoked - Docker is invoked directly for other Jobs (
codeinteland native executionbatches) - The directory containing the repository is mounted to the container.
- "Steps" are ran in sequential order.
- If the Job is
- The container run a defined command against the repository.
- Logs from the container are sent back to the executor.
- Logs are streamed from the executor to a Sourcegraph API
- The executor calls a Sourcegraph API to that "complete" the Job.
Refer to the Troubleshooting Executors document for common debugging operations.